Cybersecurity Today
Cyberattacks
Worms - exploits security vulnerabilities and spreads automatically through networks
Trojan Horses - malicious program that appears harmless
Viruses - a program that can copy itself and infect computers via networks or other medium
There’s also the risk that someone exploits a vulnerability and personally accesses private information such as account numbers.
Cybersecurity
Encryption - a way to send message from one machine to another in code; the only person able to decode the message is the person with the correct key; promotes confidentiality
Firewalls - constrain the use of systems and networks by blocking services, preventing malicious programs to enter a network; incoming packets that are flagged are not allowed through; disallows FTP connections to computers on the Internet
Antivirus Software - scans files and eliminates computer viruses and malicious software; refers to a list of known viruses that should be constantly updated
Technological Examples and Background
Stats
Over 1000 cyber-trained FBI employees domestically
43% - number of organizations that say that cybersecurity is part of their risk management
40% - increase in cyberattacks on Federal networks in 2010, according to a White House report to Congress
45% - estimated number of organizations that do not budget for cybersecurity
42% - estimated number of organizations that do not have an information security policy
49% - number of organizations that list budget constraints as the primary issue in implementing computer security

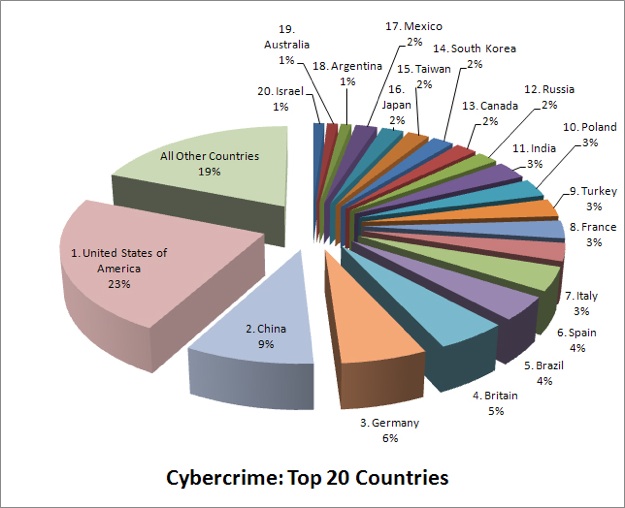
Looking Globally
In the modern global economy, consumers, businesses and governments are all dependent on computing and information processing services that take place over information networks.
U.S. Domestic Policy Initiatives
Here are a few examples of current U.S. policy reactions to cyber security challenges today...
Obama’s Cyber Czar
In his first term President Obama created the position of Cybersecurity Czar: a senior White House Official who will have broad authority to develop strategy to protect the nation’s government-run and private computer networks.
The Rockefeller-Snowe Cybersecurity Act - National Cybersecurity Insurance
Senators Jay Rockefeller, D-WV, and Olympia Snowe, R-Maine, have introduced a bill that mandates President Obama, or his apointee, to report to Congress on “the feasibility of creating a market for cybersecurity risk management” within one year of the bill’s passing.
The Lieberman Act
A bill introduced by Senator Joe Lieberman, I-Conn, seeks to establish a National Center for Cybersecurity and Communications under the Department of Homeland Security.
Journal of Information Management and Computer Security
Information systems, security issues, and decisions for small businesses
by Atul Gupta and Rex Hammond
“While their motives may vary, individuals planning an attack have a wide array of attack options. Erasing a customer data base, planting a virulent virus, rifling through correspondence files, sending a Trojan Horse, copying personnel records and searching for active credit card numbers are just a few of the attacks that may be directed at the victim’s information technology (IT) system.”
“The use of IT has become more widespread and today’s organizations rely on information systems (IS) to the extent that it would be impossible to manage without them. The growth of e-business and e-commerce applications also presents abundant opportunities for unauthorized access to IS“
As the users of products and services provided by government and business that use our valuable private information like account numbers, contact numbers, social security numbers and more and more of our shopping and correspondence, being transmitted over cyberspace, consumers and citizens are at risk of becoming victims of cyberattack. U.S. online retail reached $175 billion in 2007 and is estimated to grow to $334.7 billion by 2012. Online banking has become a new norm offered by almost all national banks, and 40% of dollars traded in the NASDAQ market are made over electronic communication networks.
Consumers and Individuals
Networks and access points enable businesses to store information, transmit information to coordinate branches of global companies, carry out financial transactions, and manage large volumes of trade and customers. This information and it’s proprietarity is crucial to modern business operations, privacy for consumers and company competitiveness. A market for cyber security products like anti-virus software has emerged in the US, funding product development in the private sector. More and more companies have IT teams today than ever before, but small businesses often struggle to find the funding to improve their information systems.
Businesses
Government
The government relies on networks for communications, control of infrastructure like power grids, and the processing and registry of data used in many of its services offered to citizens. The department of defense stores volumes of classified material on computers within certain networks that is crucial for our intelligence and foreign policy.
Food for Thought!
Public school students are required to have vaccinations, because, if one student doesn’t get a vaccine and gets sick, that students puts everyone else at risk - Should the government could take a similar approach to cybersecurity? Mandating certain levels of protection for anyone who chooses to use the internet? How could it go about implementing this?
Cybersecurity is a global problem - other countries struggle with the same vulnerabilities that the United States deals. Recent cyberattacks (see Case Study 2!) across country borders demonstrate the global scope of this issue. Here, we look at some examples of activity in the world of cybersecurity across the globe:
European Union
“Cyber Europe 2010” took place among member states in the EU in November 2010. Since the EU member states are all part of a large cyberinfrastructure, they worked on establishing trust between members and used practice exercises to identify vulnerabilities in incident management. The EU has also begun to prepare for mutual support procedures in the case of massive cyberattacks or incidents. The United States could learn from this practice and begin to a establish a stronger contingency plan in the case of a large-scale attack. (source)
Malaysia
In Malaysia, an agency called “CyberSecurity Malaysia” is responsible for looking after the safety of Malaysia cyberspace. CyberSecurity Malaysia conducts a large amount of services in order to improve the cyber-climate of the country. They run a help center and encourage citizens to contact them to get in touch with a cybersecurity speacialist. They run a training center and examination center for international certification of cybersecurity professionals under the belief that the country needs more professionals working in the field. CyberSecurity Malaysia even develops educational content for various age groups (from students to office workers) and provide a free download for all interested parties. This contrasts with the American model where there is not one single government-funded body responsible for overseeing cybersecurity, which can make it more difficult to take action or properly monitor cyberspace. (source)
In general, most countries are struggling with issues of cybersecurity like the US. Aside from a lack of funding and lack of publicity to the issue, there is not clear best practice for combatting cybersecurity concerns or improving cyberinfrastructure.
China
China-based hackers have become a very significant part of the cybersecurity threat in the United States. They have compromised security at Google and Yahoo, and have even allegedly successfully compromised portions of the US power grid. Because of the global nature of the Internet and our information systems, we need to be aware of the issue of global cooperation in regards to cyberinfrastructure issues, as China’s current cyber-environment allows for these sorts of acts to be conducted. For more on this story see NY Times.

But these parties traditionally have not worked together...